This guest post is written by Mayank Choudhary, Vice President of Products, ObserveIT
According to a recent Verizon DBIR report, 90% of all security issues stem from insiders, whether intent is malicious or accidental. With increasing attention being placed on the risks associated with vendors, consultants, privileged users, high-risk employees and everyday business users, there is no doubt organizations must implement processes and technology to combat insider threats. But what are the problems that are causing the most concern for organizations as they struggle to put an effective Insider Threat program in place?
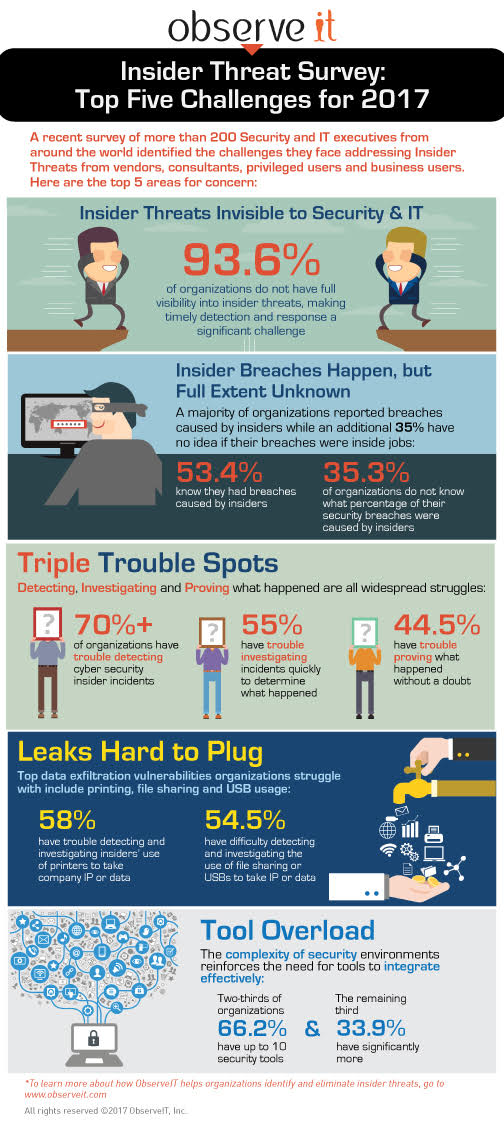
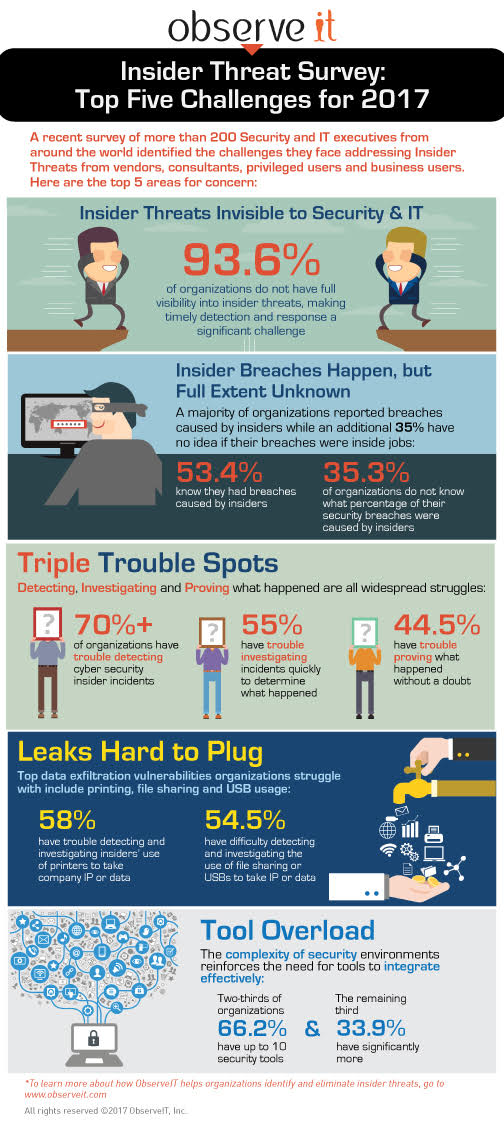
A recent survey by ObserveIT of more than 200 Security and IT executives from around the world set out to identify the top five challenges companies face when addressing Insider Threats – here are the results:
Security & IT Need Visibility: 93.6% of organizations do not have full visibility into insider threats, which makes it a significant challenge to ensure privileged users, consultants, vendors and business users are not violating security policies.
Full Extent of Insider Breaches is Unknown: Most organizations (53.4%) reported they had breaches caused by insiders, but an additional 35% do not know what percentage of their security breaches involved insiders.
Detecting, Investigating and Proving What Happened Are All Trouble Spots: More than 70% have difficulty rapidly detecting cyber security incidents, 55% report trouble investigating incidents in a timely manner, and 44.5% have trouble gathering irrefutable proof of what occurred.
Top Data Exfiltration Vulnerabilities include Printing, File Sharing and USBs: 58% of organizations cite detecting and investigating the use of printers to take company IP or data as a trouble spot, and a majority (54.5%) say they have difficulty detecting and investigating the use of file sharing or USBs to take data.
Tool Overload a Concern: Security environments are very complex, with 66.2% of organizations having up to 10 different security tools and 33.9% having many more. This points to the importance of selecting tools that integrate seamlessly, which can be a challenge.
Summary: The bad news is that the overwhelming majority of organizations are struggling when it comes to identifying and eliminating risks created by the negligent or malicious activities of privileged users, consultants, vendors and business users.
But the good news is that more and more organizations are realizing that they need to evolve their security postures from primarily worrying about external threats to a balanced approach that addresses their biggest security vulnerability – insider threats. This increased focus on real-time detection and response to security breaches caused by insiders is not only of great benefit to their organizations, it is fueling demand for effective insider threat monitoring and analytics solutions.
For more information visit www.observeit.com


















