LEGACY DLPS ARE AT A BREAKING POINT
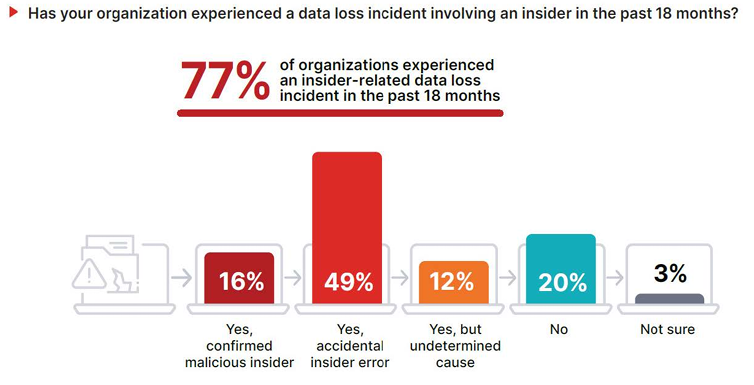
Data protection is one of the most difficult challenges in enterprise security. Intellectual property, financial records, and customer data flow constantly across SaaS apps, enterprise cloud drives, and endpoints – exposed not only to external attackers but also to insiders, whether malicious or simply careless. Many of today’s most damaging breaches stem not from perimeter compromise but from everyday business activity. In fact, 77% of organizations reported insider-related data loss incidents in the past 18 months, with 58% experiencing six or more incidents, underscoring how routine these risks have become [2025 Fortinet Data Security Report].
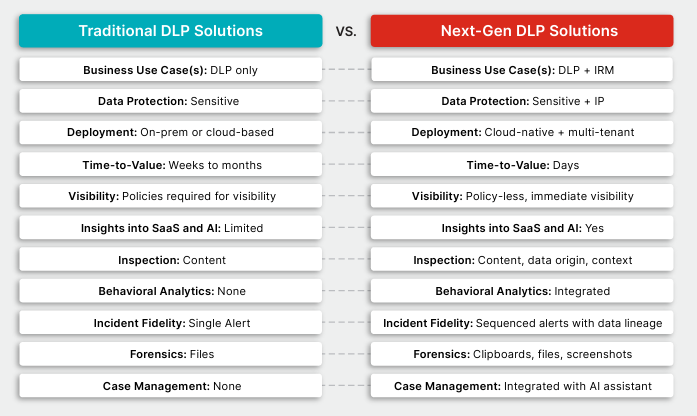
Legacy DLP was never designed for this reality. Policy-dependent, perimeter-focused tools generate excessive or unmanageable noise without context or high-risk activity sequencing, drowning security teams in alerts while sensitive data continues to leak through legitimate workflows. The “discover and classify first, protect later” model is costly, inefficient, and too slow to keep pace.
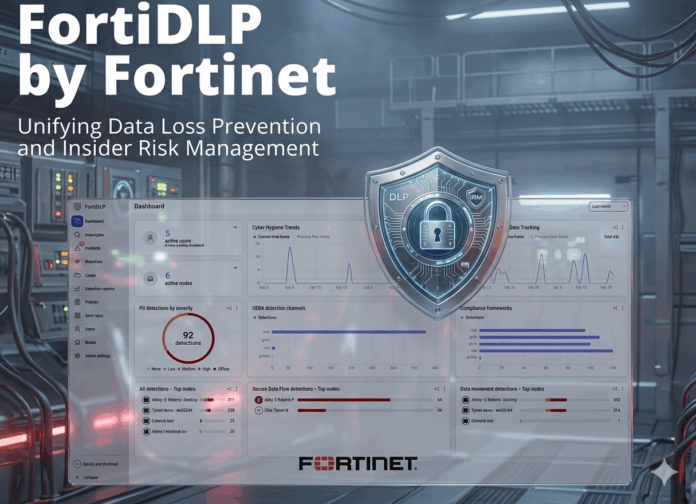
FORTIDLP’S BEHAVIOR-AWARE APPROACH
Fortinet’s FortiDLP takes a different approach, one that is a direct response to the challenges associated with traditional DLP solutions. As a next-generation, cloud-native, integrated DLP and Insider Risk Management solution, it delivers immediate visibility into data flows and exposure risks, baselines user and organizational behavior through embedded machine learning to anticipate and prevent data leaks, and applies adaptive controls, such as just-in-time user coaching, to reinforce proper cyber hygiene at the moment of risk.
FortiDLP replaces noisy static rule sets with a practical, visibility-first data control system built for hybrid work, GenAI adoption, and insider-risk defense by unifying data loss prevention, insider-risk management, SaaS data security, and risk-informed user education. It also represents a critical tool for helping organizations mature their insider risk efforts and programs.
CORE CAPABILITIES AND DIFFERENTIATORS
FortiDLP is built on a set of data security principles that directly address the gaps that make legacy DLP deployments stall or fail:
• Immediate Visibility and Protection Without Discovery Drag:
FortiDLP provides day-one visibility and control through its endpoint agent and enterprise cloud drive connectors, skipping months of data discovery, manual content classification and static policy tuning that stall most legacy DLP deployments. This is due to FortiDLP’s ability to perform content-level inspection and apply context in real time when users engage files with sensitive data. By “Protecting first, fine-tuning later,” teams can prevent both deliberate exfiltration and accidental leakage as early as possible.
• Continuous Endpoint Monitoring & Real-Time Data Identification:
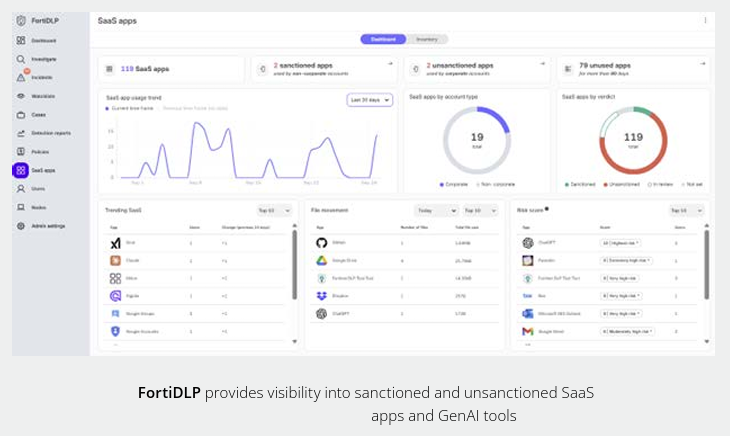
The FortiDLP agent inspects activity at the moment of data creation or access across Windows/macOS/ Linux-based endpoints, covering clipboard, web, email, print, USB, and enterprise cloud drives (e.g., Microsoft 365, Google Workspace, Box). Because the lightweight agent inspects on-device, data is protected consistently whether employees are in the office, remote, or traveling. Dynamic policies close blind spots left by legacy appliances that only see traffic after it leaves the device. FortiDLP also builds a risk-scored inventory of SaaS and AI applications in use, tracks ingress, egress and credentials, and nudges employees toward sanctioned tools when risky activity is detected.
• Secure Data Flow with Data Lineage: Origin and Identity-Aware Enforcement:
FortiDLP traces content origin (e.g., HR exports or source-code downloads) and applies policies that distinguish corporate vs. personal data egress. It enforces policies based on whether a corporate or non-corporate account is used, giving analysts a complete, auditable history of the “what, where, who, and how” of data movement. It also detects data manipulations such as file renaming, data archiving, changes to file extensions, and suspicious file movements. This lineage tracking accelerates investigations by showing the full journey of sensitive data.
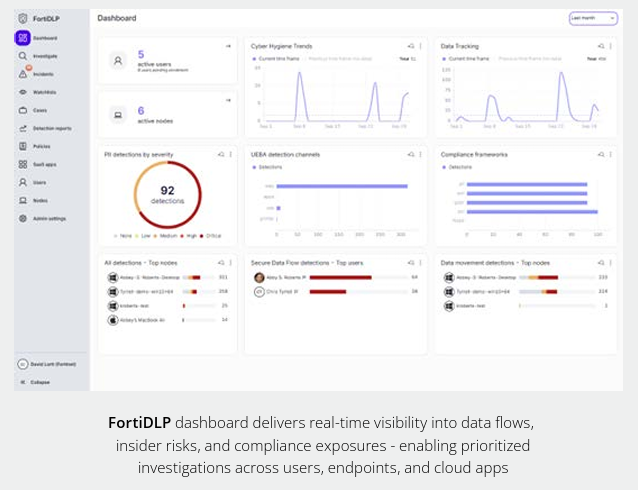
• AI-powered Behavioral Analytics and FortiAI Assistant:
FortiDLP uses embedded machine learning to establish baseline behavior for both individuals and organizations directly on the endpoint. Insider Risk Sequence Detection identifies when unusual activity occurs and automatically sequences high-risk actions by a user entity into risk-scored incidents mapped against the MITRE Insider Threat TTP knowledge base. Analysts receive full context—before, during, and after—through a time-sequenced activity feed and integrated case management. Forensics stored in the Evidence Store, including file, clipboard, and screen capture artifacts, are available on demand. FortiAI Assistant then distills the incident into a clear, concise narrative, speeding up investigation and response.
• Risk-Adaptive Realtime Response Actions & User Coaching:
FortiDLP enables precise, gradual enforcement—from auditing, real-time user coaching (via endpoints, Teams, and Slack messaging), and file egress blocking to screen, clipboard, file capture, process termination, and device quarantine/locking. Unlike legacy tools that rely on binary block-or-allow rules, FortiDLP supports business-aligned, proportional responses tailored to the severity of the risk. This adaptive approach prevents misuse without disrupting legitimate workflows. Agent and enterprise cloud drive policy enforcement is conducted on and off the network.
• Governance of Shadow SaaS and Shadow AI/GenAI Usage by Blocking Uploads of Sensitive Content:
FortiDLP delivers comprehensive visibility into how users interact with data in the cloud, maintaining protection as data moves across environments. Sensitive information remains continuously protected, regardless of its location or method of access. The solution builds a risk-scored inventory of SaaS applications and GenAI tools used across the organization, providing actionable insights into data ingress, egress, and credential usage. This visibility not only strengthens defenses against data breaches stemming from unauthorized or Shadow IT usage but also enables employees to securely adopt approved SaaS and GenAI tools—maximizing productivity while minimizing risk. In addition, FortiDLP policies can collect artifacts such as screen captures, clipboard captures and file copies.
• Privacy-First Controls:
FortiDLP stores forensic artifacts, such as shadow file copies, clipboard content, and screenshots, in customer-managed secure object storage. Built-in RBAC-managed PII pseudonymization helps meet strict privacy requirements while keeping sensitive evidence under customer control. These features align with GDPR, CCPA, PCI DSS, HIPAA, ISO 27001, and NIST standards, removing the sovereignty and compliance barriers that often stall legacy DLP deployments. Prebuilt PII/PHI/PCI policy templates accelerate rollout, and integrated authorization workflows ensure privacy-by-design investigations.
Together, these features transform DLP from a static rulebook into a live, AI-assisted risk management system that adapts to how people actually work.
COMMON USE CASES FOR FORTIDLP
These capabilities translate into real-world use cases that CISOs consistently prioritize:
- Prevent data loss from exfiltration and accidental leakage
- Monitor insider threats and high-risk employee activity
- Secure sensitive data flowing through SaaS and cloud apps
- Govern Shadow AI/GenAI usage by blocking uploads of sensitive content
- Apply behavioral analytics at scale to detect anomalies and intent
- Coach users in the moment to improve data handling practices
- Support comprehensive incident investigation, artifact collection, and case management
- Meet data security and compliance requirements (GDPR, HIPAA, PCI DSS, ISO 27001, NIST, other)
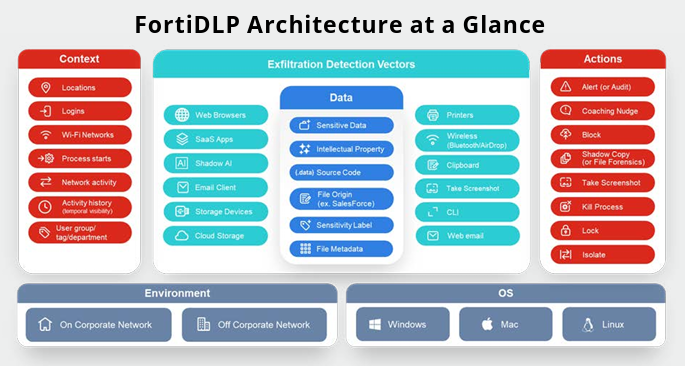
HOW FORTIDLP WORKS
Deep and broad contextual visibility is critical to protecting sensitive data, especially considering its increased use by employees to be productive.
FortiDLP operates as a cloud-native unified DLP and Insider Risk solution supported by lightweight Windows, macOS, and Linux agents and enterprise cloud drive connectors for Microsoft 365, Google Workspace, and Box.
The agents inspect data directly at the point of use, applying classification and behavioral analysis locally before sending enriched events to the FortiDLP console. The console is the central hub, where events are correlated, risks prioritized, and policies managed. Continuously updated, it gives administrators a single interface that unifies behavioral analytics, reporting, and automated response actions.
• Agent-Local Analysis:
Sensitive content is inspected directly on the endpoint, avoiding the need to forward files to the cloud and resolving data residency objections. This stands apart from cloud-only DLP models that centralize inspection and often raise data residency challenges. It also eliminates the overhead of cloud-based file scanning, reducing bandwidth costs and minimizing CPU/memory impact while scaling efficiently across enterprise fleets.
• Customer-Controlled Evidence Storage:
Shadow copies and screenshots are stored in customer-managed object storage (on-prem MinIO or AWS/GCP cloud buckets), not Fortinet’s infrastructure. This ensures organizations retain full custody of their most sensitive evidence.
• Open Integration & Automation:
FortiDLP integrates with your existing security and identity ecosystem via native directory integration, MDM profiles, event streaming, webhooks, and an open API. This enables connections not just to SIEM and SOAR platforms (FortiSIEM, FortiSOAR, Splunk, Sentinel) but also to IAM systems and ITSM/service desk tools, closing the loop between detection, response, and remediation.
• Regional SaaS Hosting:
Customers can elect to deploy the solution in their preferred region (such as Australia, EU, KSA, Qatar, and the US) to meet local data sovereignty requirements.
When paired with Fortinet’s broader Security Fabric, FortiDLP extends unified visibility into the data layer, linking users, endpoints, SaaS apps, and sensitive content into one ecosystem.
SCALABLE ARCHITECTURE FOR DISTRIBUTED OPERATIONS
Legacy DLP has been synonymous with delays and complexity. FortiDLP breaks that cycle with transparent packaging and rapid deployment paths aligned to operational maturity and compliance needs.
• Core: Best-in-class Endpoint DLP for clipboard, web, email, print, USB, and cloud-drive monitoring. Best for organizations addressing regulatory compliance and seeking fast visibility into sensitive data exposure with minimal overhead.
• Advanced: This license adds UEBA, Insider Risk Management, FortiAI, and full SaaS application visibility (Microsoft 365, Google Workspace, Box). It is ideal for teams prioritizing behavior-driven detection and reducing repeat risk through user coaching features.
• Advanced Premium: Includes all Advanced features plus regional PoPs (such as Australia, EU, KSA, Qatar, and the US) and managed services. Suited for global, regulated or resource constrained organizations requiring strict data residency and operational support.
A Best Practices Service (BPS), required for new customers, and fully Managed Advanced service offering are also available, combining platform capabilities with expert-led oversight for organizations that want outcomes without the operational lift.
OUR VERDICT
FortiDLP redefines what modern DLP should be: fast to deploy, smart enough to distinguish misuse from mistakes, and flexible enough to fit real-world operations – not just compliance checklists.
Its cloud-native architecture, AI-enhanced analysis, and human-aware enforcement stand in sharp contrast to the rigidity of traditional DLP tools. With 77% of organizations reporting insider-driven data loss in the past 18 months [ 2025 Fortinet Data Security Report ], FortiDLP’s context-rich, behavior aware model makes it a timely and strategic control for any CISO confronting insider risk, AI misuse, and today’s hybrid work realities.
___
LEARN MORE
https://www.fortinet.com/products/fortidlp
Free demo:
https://www.fortinet.com/demo-center/fortidlp-demo
Data sheet:
https://www.fortinet.com/content/dam/fortinet/assets/data-sheets/fortidlp.pdf
___
ABOUT CYBERSECURITY INSIDERS
Cybersecurity Insiders delivers strategic insight for cybersecurity leaders, grounded in independent research and trusted by a global community of 600,000+ professionals. Our research distills industry intelligence into actionable guidance for decision-makers. CISO Survey Reports reveal emerging risks and readiness gaps. CISO Guides translate those findings into strategic responses. Product Reviews evaluate the technologies that put those strategies into practice. Each review is analyst-written, outcome-focused, and designed to help security leaders assess solutions with confidence. Learn more at https://cybersecurity-insiders.com
Join our LinkedIn group Information Security Community!