This review examines TXOne Stellar, a purpose-built endpoint security solution designed for industrial OT environments. Stellar delivers prevention-first protection for air-gapped, legacy, and resource-constrained systems, balancing security needs with the operational realities of manufacturing and critical infrastructure.
THE UNIQUE DEMANDS OF OT SYSTEMS
Operational Technology systems, such as programmable logic controllers, CNC machines, SCADA terminals, and operator workstations, form the backbone of manufacturing and critical infrastructure. These systems often run legacy operating systems, such as XP or 2000, operate within segmented networks, and require absolute operational reliability. Unlike office IT environments, OT systems cannot tolerate unexpected reboots, resource-heavy scans, or cloud-dependent security updates that might interrupt production.
These same systems face escalating threats, including ransomware targeting industrial networks, supply chain attacks via USB devices, and insider threats that exploit configuration changes. Traditional endpoint security is designed for always-connected environments but often fails catastrophically in these environments. The result? Critical industrial assets remain exposed because installing conventional security agents poses greater operational risk than the threats themselves.
Industrial environments need endpoint security that works within operational constraints, not against them. TXOne Stellar takes a prevention-first approach that blocks ransomware, unauthorized changes, and malicious files before they can impact operations—all without requiring system modifications, internet connectivity, or forced updates.
PURPOSE-BUILT PROTECTION FOR INDUSTRIAL REALITIES
TXOne Stellar addresses the unique demands of industrial endpoints through three core capabilities:
• Universal compatibility across Windows 2000 through Windows 11, including legacy systems in airgapped and resource-limited environments
• Zero-impact deployment with no reboots required, no forced updates, and no internet dependency
• Operations-friendly controls that empower both security teams and field operators without disrupting critical processes
Consider a pharmaceutical plant running validated processes on Windows 2000 controllers—systems that cannot be modified without triggering costly re-validation. Or a power generation facility where a single unplanned reboot could result in millions of dollars in lost production. Traditional antivirus software becomes a liability in these environments, often rejected by operations teams that have experienced system crashes from overly aggressive security tools. Many facilities still rely on USB transfers for updates, and due to network isolation this creates security gaps that conventional solutions cannot address.
PROTECTION DESIGNED FOR INDUSTRIAL CONSTRAINTS
Stellar’s comprehensive Windows support, from Windows 2000 SP4 through to the latest releases, reflects the reality that industrial environments often run diverse, out-of-support systems. This isn’t an afterthought or a premium add-on for Stellar; it is core functionality designed specifically for organizations that cannot simply “upgrade to the latest version.”
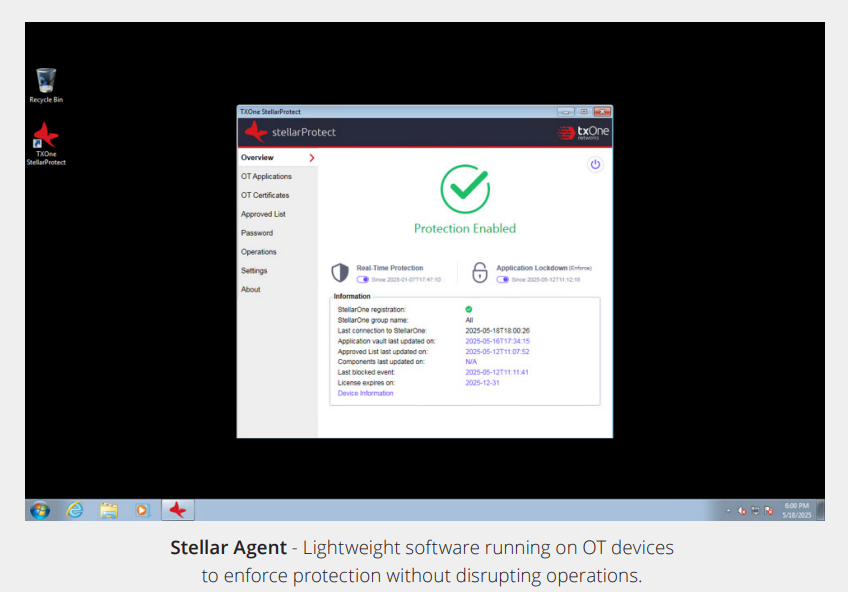
Deployment follows operational requirements: installation completes in 2 to 70 minutes, depending on configuration needs, with no system restart required. The lightweight agent uses minimal CPU and memory, which is essential for resource-constrained industrial computers. Offline deployment packages support air-gapped environments, while deferred update options ensure patches never interrupt production schedules.
Stellar’s Cyber-Physical Systems Detection and Response (CPSDR) technology monitors both file integrity and operational behavior patterns. For example, if an unauthorized script attempts to modify OT application files outside normal maintenance windows, Stellar blocks the action, even without a matching malware signature. This behavioral approach catches zero-day threats and insider risks that signature-based tools miss.
The platform automatically inventories installed applications, certificates, and scripts, creating behavioral baselines without manual configuration. This auto-learning capability reduces deployment time from weeks to days or hours while ensuring legitimate operational changes aren’t blocked. For organizations with hundreds of unique industrial systems, this automation eliminates the traditional trade-off between security and operational flexibility.
Stellar includes critical operational safeguards, such as maintenance mode for planned system updates and an emergency stop for immediate threat response. These features, developed through collaboration with plant operators, build trust by ensuring security never becomes an operational obstacle. As one plant operator noted: “Finally, security that respects our need for control.”
Key protection capabilities include:
• USB device control preventing malware introduction through removable media
• File integrity monitoring blocking unauthorized system changes
• Flexible scanning schedules aligned with maintenance windows
• Compliance reporting for NERC CIP, IEC 62443, and sector-specific standards
SCALABLE ARCHITECTURE FOR DISTRIBUTED OPERATIONS
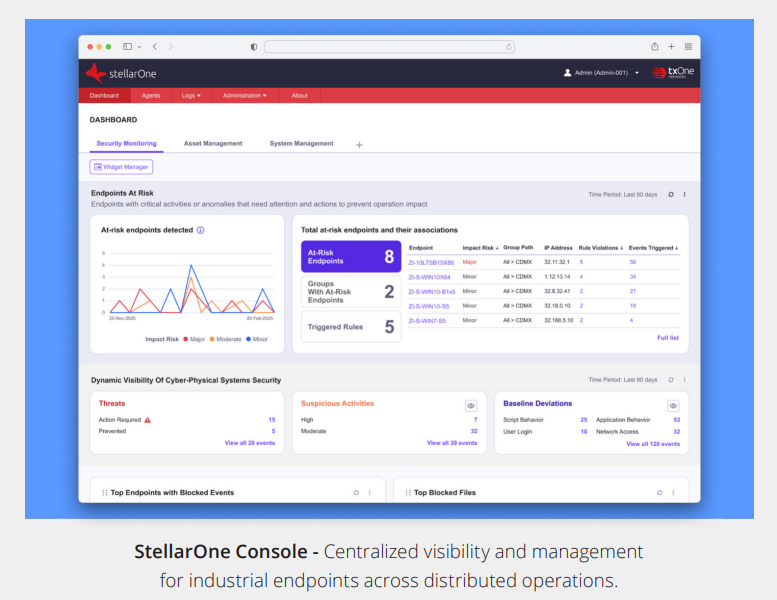
The Stellar platform employs a two-tier architecture that balances local protection with centralized visibility. This design enables effective security across geographically distributed sites, hybrid IT/OT networks, and offline facilities that addresses the fragmented nature of industrial environments.
• Stellar Agent: Available in variants optimized for modern and legacy Windows systems. The legacy agent specifically addresses limitations of older operating systems, ensuring Windows 2000 and XP systems receive the same protection level as modern endpoints. Agents operate autonomously when disconnected from the console, maintaining protection during network outages or in permanently air-gapped environments.
• StellarOne Console: Deployed as a virtual appliance on-premises (VMware, Hyper-V, KVM) or in private clouds (AWS, Azure). Manages up to 30,000 endpoints with role-based access controls, automated policy distribution, and SIEM integration. The console’s hybrid management model enables security teams to establish enterprise policies while providing operators with local override capabilities when necessary.
This architecture delivers security without infrastructure dependencies. Organizations can protect isolated plants, mobile equipment, and remote sites with the same policies and visibility as they do for connected facilities. For companies with global operations, this flexibility proves essential.
LONG-TERM PROTECTION FOR LONG-TERM ASSETS
Console deployment takes approximately 10 minutes, with agent rollout completing in under an hour, even with full baseline scanning. More importantly, Stellar’s lifecycle protection model aligns with industrial reality by dependably supporting systems that may operate unchanged for 10-15 years. This commitment to long-term support differentiates Stellar from consumer-grade and IT-based solutions that abandon older platforms after 3-5 years.
TXOne offers licensing aligned with deployment scenarios:
• Stellar ICS: Annual subscription for comprehensive industrial endpoint protection
• Stellar Kiosk: Specialized licensing for fixed-function terminals and operator interfaces
• Stellar OEM: Perpetual licenses for equipment manufacturers embedding protection into industrial products
Organizations across manufacturing, energy, and critical infrastructure deploy Stellar to protect legacy controllers, SCADA systems, and operator workstations. The solution’s combination of zero-impact operation, offline capability, and operational controls makes it particularly valuable where availability requirements exceed 99.9%.
BRIDGING THE SECURITY-OPERATIONS DIVIDE
Stellar addresses a fundamental challenge in industrial cybersecurity: protecting critical systems without disrupting critical operations. By supporting legacy systems as they are, rather than deprecating them, Stellar extends asset lifecycles while maintaining security. The solution’s lightweight design, flexible deployment options, and operator-friendly controls demonstrate an understanding of industrial realities that purely IT-focused tools fail to address.
For organizations seeking endpoint protection that operations teams will actually accept and use, Stellar represents a significant advancement in industrial security design.
LEARN MORE
• TXOne Stellar product page: https://www.txone.com/products/endpoint-protection/stellar/
• Schedule a demo or speak with sales: https://www.txone.com/contact/
• Watch Stellar in action:
› Security for Legacy OT Systems Made Possible: https://www.youtube.com/watch?v=yuXJBraTfpQ
› Seamless Journeys Start With Secure OT Environments: https://www.youtube.com/watch?v=wuPkUnN6bHk
__
ABOUT TXONE
TXOne Networks specializes in cybersecurity solutions designed specifically for operational technology environments. Working with global manufacturers and infrastructure operators, the company develops security technologies that protect industrial operations without compromising availability or performance. TXOne’s portfolio spans network defense, endpoint protection, and inspection tools—all engineered to work within the unique constraints of industrial systems.
Join our LinkedIn group Information Security Community!