

OK, we had some fun, and now let’s get serious. Here’s my list of the presentations I found to be the most interesting and/or educational from last week’s security conferences in Vegas.
Favorites
1: Black Hat: Understanding and Exploiting Implanted Medical Devices: Taking the torch from Barnaby Jack, researchers Billy Rios and Jonathan Butts not only revealed critical vulnerabilities in insulin pumps and pacemakers, but also focused on responsible disclosure and the less-than-stellar handling of exposed vulnerabilities by the affected vendor. A true demonstration of the alarming lack of security focus on behalf of medical device manufacturers. Standing ovation!
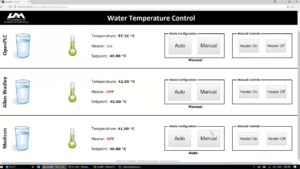
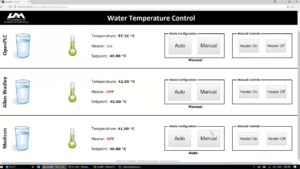
2: DEF CON: Hacking PLCs and Causing Havoc on Critical Infrastructures: Programmable Logic Controllers (PLCs) are used throughout our factories and critical infrastructure (including nuclear power plants). Thiago Alves demonstrated just how easy it is possible to prevent PLCs from responding to operator’s instructions and even “brick” some of them. Outdated/unsecure protocols used in PLC communication are the main culprit.
3: Black Hat: AI & ML in Cyber Security – Why Algorithms are Dangerous: Excellent presentation by Raffael Marty from Forcepoint that cut through the FUD of Machine Learning (ML) and Artificial Intelligence (AI) as the “silver bullet” of the security industry. From cognitive biases to being susceptible to adversarial inputs, ML is not the be-all and end-all for cybersecurity. Yes, algorithms are getting “smarter”, but the Marty argues that human experts are more important.
Honorable mentions go to these presentations due to their focus on unique attack vectors:
1: DEF CON: barcOwned — Popping shells with your cereal box: The talk focused on what can be done using malicious bar codes to barcode scanners themselves, but more importantly, to the computers those scanners are connected to. And you thought you can unwind and lower your “shields” at least when buying a carton of milk or a six-pack? Think again! And, by the way, there is currently no way to secure scanners from being programmed via bar codes…
2: DEF CON: What the Fax!?: Speaking of unique attack vectors, this was an equal parts hilarious and scary presentation about those relics of the 20th century called fax machines that are still in use, believe it or not. Specifically, all-in-one printers that include the fax feature. TL;DR fax can be used as a gateway to internal networks. Unplug!
(Note: to view this presentation, follow this link, search for the word “fax”, and download the slide deck using ‘Save Link As’ option).
3: DEF CON: Please do not Duplicate: Attacking the Knox Box and Other Keyed Alike Systems: Let’s not forget about the physical world! Knox box provides non-destructive emergency access to commercial and residential properties to be used by fire departments, police and paramedics. What could possibly go wrong when someone tries to backdoor an entire city by 3D printing a key to those Knox boxes?
What presentations stood out to you last week? Leave a comment on our Twitter or LinkedIn.



















