Digital Certificates are virtual IDs that represent users, machines, servers, and the like in the digital landscape. A user’s attributes can be input onto a certificate and issued to that user’s device, verifying that user’s identity whenever they access the network.
Digital Certificates are vastly superior mechanisms of authentication security when compared to passwords because they use the power of Public Key Cryptography. Replacing passwords with certificates means leaving behind annoying password reset policies and the looming threat of a stolen password.
Implementing certificates is a commitment because it requires building a Public Key Infrastructure (PKI), but the benefits that certificates bring are worth the labor. Below, we’ve listed more reasons why certificates are vital for network security and productivity.
Certificate Use EAP-TLS to Eliminate MITM Attacks
According to IBM’s X-Force Threat Intelligence Index, man-in-middle (MITM) attacks are one of the most common forms of cyber attack, comprising 35% of exploitation activity. Unsecured Pre-Shared Key Wi-Fi is one of the biggest reasons MITM attacks have become one of the most popular attack vectors. Public Wi-Fi areas are goldmines for hackers, as they can set up rogue hardware, spoof the legitimate SSID, and trick users into connecting and sending over credentials.
Certificates can prevent MITM attacks from happening because they encrypt sensitive data and use EAP-TLS authentication. EAP-TLS is the most secure IEEE 802.1X protocol because credentials aren’t sent over-the-air. Instead, they are used to enroll for certificates issued by a trusted Certificate Authority (CA). Password-authentication forces you to send sensitive credentials over the air thousands of times a day, certificates eliminate the need for this.
Certificates can be used to identify every network object. This means that it gives you a guaranteed identity and device for every network connection on your network.
Certificates Provide Identity Context for Zero Trust Network Access
A Zero Trust Network is a network designed to adhere to the security philosophy of Zero Trust. In the past, network admins designed their networks to give high levels of access to users who were in the network, as it was assumed that users with network access were trustworthy. The Zero Trust philosophy changes this, assuming that even network users are not trustworthy, forcing admins to rethink the levels of access they give to their network users.
Since Zero Trust requires access to be given on a per-need basis, to authorized individuals, understanding the identity of devices accessing the network is imperative, admins need to ensure their resources are secure by enforcing strict access control and establishing Identity Context. Since new web and cloud applications are introduced constantly, admins need a dynamic solution to identify and segment users based on access levels.
Certificates can provide Identity Context in a Zero Trust network because user attributes can be input and encrypted onto a certificate and serve as their digital identifier.
Investing in Certificates Increases Security Across the Organization
Certificates don’t have to be used for one specific purpose. One certificate can be used to secure multiple domains, servers, and workstations. One certificate can authenticate a user for office Wi-Fi access, VPN access if they work remotely.
While certificates require a Public Key Infrastructure (PKI) in order to operate, a PKI can be used to secure tons of applications with certificate-based authentication. Plus, with an easy-to-use cloud solution like SecureW2, you can integrate with your existing CA or create your own PKI from scratch, vastly reducing the cost of security.
Some examples of applications that can use certificates instead of passwords are Wi-Fi, VPN, Web Apps, Desktop Logon, SSH, and Document Signing.
Certificates are Easier on the End User
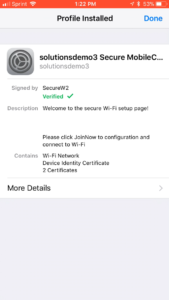
While certificates can be complex and hard to understand, they don’t really need to be understood by the end user in order to work. By leveraging onboarding software like SecureW2, users can download an app and follow a quick setup tutorial. A signed certificate will be automatically provisioned to that user’s device and they only pressed a few buttons. Below is an example video of what this process would look like for end users:
Certificates eliminate the need for password-change policies as well. In Higher Education environments, the average user has around 7-10 internet connected devices. Forcing them to re-configure their devices every 60-90 days, is a terrible user experience, especially in a high-pressure scenario such as University.
Certificates Eliminate 30-50% of Connectivity-Related Support Tickets
IT departments are dedicated to addressing technical issues that students experience, but it forces them to divert attention away from value-add tasks. A massive amount of support tickets can tank productivity. If the problem gets severely out of hand, IT admins might have to work overtime or outsource for temporary help.
40% of the IT Service Desk volume consists of password-related issues, according to the InfoTech Research Group. As stated before, certificates remove the need for passwords and password reset policies, a common cause for sudden influxes of support tickets. The average customer that switches from Wi-Fi passwords to certificates with SecureW2 reduces their connectivity tickets by 30-50%, vastly reducing the overhead required for the IT helpdesk.
So there you have it, 5 Reasons to Implement Digital Certificates for Network Authentication. Do you want to use certificates? With SecureW2’s Managed PKI solution we make it really easy to distribute and manage certificates. By integrating our software with your current PKI infrastructure or creating a new PKI with us, deploying certificate-driven security will be safe and easy to manage. Check us out at www.securew2.com if you’d like to learn more.