MOST POPULAR
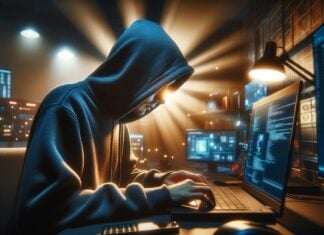
Ransomware gangs are now focusing more on speedy attacks
Over the past few years, ransomware groups have continually refined and adapted their methods, evolving from slow, opportunistic attacks into highly coordinated and efficient...