cybersecurity
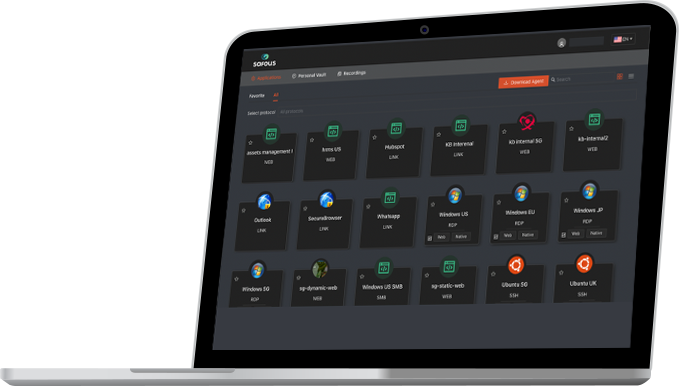
PRODUCT REVIEW: Safous Zero Trust Access
The Safous Zero Trust Access (ZTA) solution emerges as a comprehensive cybersecurity platform, designed to tackle the growing challenges enterprises face in protecting digital assets in an increasingly interconnected and dynamic world. With the rise of remote work, BYOD policies, and sophisticated cyber threats, the demand for robust, flexible security solutions is more critical than […]
The Digital Future Needs Cybersecurity Leaders
We’re sure you have heard this before: the rate of technological change is accelerating. It is unpredictable and unprecedented. As the World Economic Forum acknowledges, the fourth industrial revolution brings “developments in previously disjointed fields such as artificial intelligence and machine learning, robotics, nanotechnology, 3D printing and genetics and biotechnology [that] are all building on […]
Understanding CAT Culture in Cybersecurity: Collaboration, Awareness, and Training
In the dynamic and ever-evolving landscape of cybersecurity, organizations are increasingly recognizing the importance of fostering a robust security culture to mitigate risks and safe-guard sensitive data. One such approach gaining traction is the implementation of CAT culture, which emphasizes Collaboration, Awareness, and Training as foundational pillars in fortifying defenses against cyber threats. Collaboration: At […]
Keeping cybersecurity within focus as economic pressures take hold
[By Chase Richardson, Head of US & Lead Principal at Bridewell] The operators of US critical infrastructure are facing intense pressure due to cyber threats to their interconnected systems and networks. To bolster the sector’s defenses, the Biden-Harris Administration last year rolled out the National Cybersecurity Strategy. This comprehensive set of mandatory regulations aims […]
Beyond Technical Skills: Making Cybersecurity More Human-Centered
[By Perry Carpenter, chief evangelist and security officer, KnowBe4] If burglars were breaking into your front door every day, would you decide to protect your windows? This is what cybersecurity practitioners are doing and it makes no logical sense. Nearly 90 percent of cyber incidents are due to human error and yet only four […]
Cybersecurity trends: Some rays of hope among the dark clouds
[By Dov Lerner, Cybersixgill] Cybersecurity veterans often have a pessimistic view of the industry’s trends: attacks seem to be always on the rise, threat actors become more sophisticated, and breaches grow costlier than ever to their victims. I’m happy to note that there’s some good news for a change, as my company discovered while […]
Cybersecurity news headlines trending on Google
AT&T Acknowledges Data Breach AT&T, one of America’s leading telecom brands, has confessed to a significant data breach, revealing that sensitive information pertaining to millions of customers has been leaked onto the dark web. This breach has raised concerns about potential identity theft and other cyber-crimes among affected customers, prompting the company to take swift […]
Will AI augment or annex cybersecurity jobs?
[By Jamal Elmellas, Chief Operating Officer, Focus-on-Security] Generative AI is expected to impact 60% of jobs in advanced economies like the UK according to the International Monetary Fund (IMF), half of which will gain from enhanced productivity while the other half will take over tasks previously performed by humans, lowering labour demands, wages and hiring. […]
The Resounding Boom of Cybersecurity: Understanding Its Ever-Expanding Industry
In today’s digital landscape, cybersecurity has emerged as not just a necessity but a thriving industry. With cyber threats becoming more sophisticated and pervasive, the demand for robust security measures has skyrocketed, propelling cybersecurity into a realm of unprecedented growth and innovation. 1. Escalating Cyber Threats: The proliferation of technology in every aspect of modern […]























Overcoming security alert fatigue
Alert fatigue represents more than a mere inconvenience for Security Operations Centre (SOC) teams; it poses a tangible threat to enterprise security. When analysts confront a deluge of thousands of alerts daily, each necessitating triage, investigation, and correlation, valuable time is easily squandered on false positives, potentially overlooking genuine indicators of an enterprise-wide data breach. […]