

Author: Thomas Hazel, Founder, CTO & Chief Scientist, ChaosSearch
Creating an effective threat hunting program is among the top priorities of security leaders looking to become more proactive and build active defenses.
Yet finding the right expertise to staff a hunt team remains a challenge, with 58% of respondents in a recent SecOps survey saying they felt their organization’s investigative skills and capabilities were in need of improvement.
Organizations must adopt a structured process to guide their hunting activities. Those that rely on formal frameworks or methodologies are far more likely to detect vulnerabilities in their environments — as well as in-process malicious activities — than those that do not.
Let’s get started.
Why Employ a Formal Threat Hunting Framework?
Threat hunting is a purposeful and structured search for evidence of malicious activities that have not yet generated security alerts – it’s a human-centric activity that pushes the boundaries of automated detection methods.
While there are many different detection activities that could be considered threat hunting, ranging from simple file matching exercises to complex analytics, not all of these detection activities are of equal value.
Just starting out, security operations programs will structure their hunts to seek out evidence of particular indicators of compromise (IoC) that, for example, they may have learned about from recent threat intelligence feeds.
More mature organizations will begin to curate their IoC lists by incorporating contextual information to improve the quality of the intelligence. Some will add machine learning-aided anomaly detection to help them better understand baseline conditions in the environment. And the most mature of all will perform hypothesis-driven hunting that relies on anomaly detection and IoCs selectively as inputs that inform a more comprehensive understanding of the organization’s specific risk profile.
Just as not all detection activities are of equal value, not all IoCs are similarly worrisome if discovered. Generally speaking, the easier it is to detect an IoC, the less likely its detection is to interfere with attackers’ ability to accomplish their objectives.
Celebrated network security expert David Bianco makes this point in a graph he calls the “pyramid of pain.”
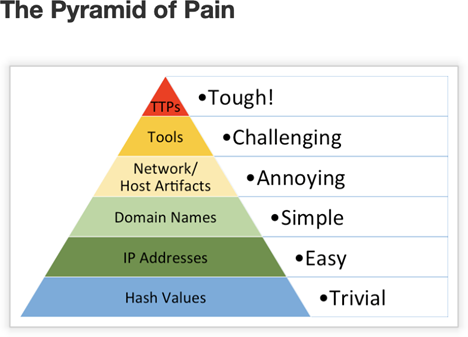
Source: Enterprise Detection and Response
The IoCs at the base of the pyramid are trivial to detect with a simple anti-malware scan. However, this finding means that attackers have successfully installed previously-discovered malware in your environment.
This is often among the earliest stages of an attack, and without evidence that further exploration of the network has taken place, doesn’t mean – in and of itself – that a major incident has occurred.
Formal threat hunting frameworks enable hunt teams to reach the top of the pyramid far more quickly and easily by providing a comprehensive library of all the steps that attackers may take in order to achieve their objectives. Relying on frameworks enables security teams to be thorough and exhaustive when hunting. Moreover, a standard methodology enables the SecOps team to ensure consistency over time in their threat hunting function, and fosters continual learning and improvement as lessons learned from each hunt are captured and used to inform future hunts.
Knowing What to Look for
Though adversaries are always seeking to enhance their capabilities by exploiting previously undiscovered vulnerabilities or honing new techniques, the majority of attacks follow the same general trajectory — from initial exploration of the victim environment, through detailed reconnaissance and attempts to gain access to privileged credentials, all the way up to data exfiltration or another means of achieving the objective.
Threat hunting frameworks help hunt teams focus on uncovering traces of the most meaningful activity patterns. Hunters can then draw upon comprehensive and relevant research and intelligence when formulating the hypotheses they’ll investigate within the hunt.
Signs of a Data Breach or Attack
In pursuing a sophisticated, long-term attack, the attackers will often:
- Combine multiple techniques within a single campaign that occurs over a relatively short time frame,
- Repeatedly attempt to gain or elevate access privileges,
- Change the contents of endpoint file systems- often with one or more endpoints as well as other network resources,
- Alter system configuration settings to deviate from what’s normal for the organization,
- Move data or suspiciously alter remote server connection patterns
The biggest challenge in threat hunting is distinguishing the “signal” — that is, true evidence of malicious activity — from “noise” — the wide range of diverse activities that take place among legitimate users across the computing environment every day. Threat hunters know that the true signals are there, hidden in the daily noise. Threat hunting is the art and science of analyzing the data to uncover these hidden clues.
Applying Threat Hunting Methodologies
Most mature threat hunting teams follow a hypothesis-based methodology that’s grounded in the scientific method of inquiry. This is an approach to knowledge acquisition that’s based on logical reasoning and empirical evidence and was designed to prevent biases and assumptions from influencing results.
Each threat hunt progresses through some version of each of the following steps.
1. Define the Attack Scenario
Rather than generally searching for various types of threats, the starting point is to define a specific, narrowly focused threat that could be underway in the environment. In this step, the hunter should think through the overall techniques that could be used, the targets within the network that could be attacked, and the various vulnerabilities that can be exploited.
2. Formulate an Initial Hypothesis
In thinking through the goals of the attacker for each stage in the attack chain, the hunter makes a series of “informed guesses” about what tools and techniques the attacker might use and what evidence might be created by their activities. The hunt is then structured to look for the evidence that would be generated if indeed each sequential hypothesis is valid.
3. Identify and Gather Evidence to Investigate each Hypothesis
Your hunt team will need to assemble the data sources that will be analyzed within the hunt. To prove or disprove a hypothesis with a high degree of confidence, multiple forms of evidence are usually needed. Hunters will also need to document where data comes from to ensure that sources are both contextualized and consistent.
4. Leverage Analytics to Reveal Results
During this stage, evidence is correlated and subject to analytical and visualization techniques to uncover relationships within it. Threat hunters need a deep understanding of adversarial tradecraft as well as what’s normal within the environment to be successful here.
5. Report Results
It’s key to document the types of evidence collected, the nature of the analysis performed, and the logic behind the conclusions that are reached while the hunt is still in process. This enables the hunt team to communicate with management as well as incident responders.
Supporting a Formal Threat Hunting Framework
Security teams making their first foray into threat hunting might do so on an ad hoc basis, but hunts will be most effective with clear goals and a well-structured process. This makes it easier to repeat the investigative strategies that have given you the best results. It also facilitates measuring outcomes, presenting findings to incident responders, and incorporating what’s learned into the organization’s automated alerting infrastructure.
Though it’s possible to conduct a hunt according to a self-designed or threat intelligence vendor-supplied framework, the vast majority of security programs rely on the MITRE ATT&CK framework. MITRE ATT&CK incorporates hundreds of known adversarial tactics and techniques into a globally accessible open-source knowledge base.
READ: How To Use the MITRE ATT&CK Framework
Putting Threat Hunting into Action
The most important threat hunting success factor is fast access to the right data, including long-term historical data. With access to the right data sources, threat hunters can use analytics tools like Kibana to carry out their hunts, running the queries and visualizations that let them draw out the important signals of a potential attack. A key step for organizations looking to improve their threat hunting capabilities is to consider investing in the data lake architectures, data cleaning, and indexing tools necessary to support the massive data requirements of threat hunting analytics.
ChaosSearch streamlines this process at scale. Threat hunters gain more insights, faster, and can spend more time hunting for malice, spend less time worrying about the accessibility data sets, and help dramatically improve the overall security posture of the organization.


















